You access an AWS service using an endpoint. The default service endpoints are public interfaces, so you must add an internet gateway to your VPC so that traffic can get from the VPC to the AWS service. If this configuration doesn’t work with your network security requirements, you can use AWS PrivateLink to connect your VPC to AWS services as if they were in your VPC, without the use of an internet gateway.
You can privately access the AWS services that integrate with AWS PrivateLink using VPC endpoints.
Overview
You can access AWS services through their public service endpoints or connect to supported AWS services using AWS PrivateLink.
This overview compares these methods.
Access through public service endpoints
The following diagram shows how instances access AWS services through the public service endpoints. Traffic to an AWS service from an instance in a public subnet is routed to the internet gateway for the VPC and then to the AWS service. Traffic to an AWS service from an instance in a private subnet is routed to a NAT gateway, then to the internet gateway for the VPC, and then to the AWS service. While this traffic traverses the internet gateway, it does not leave the AWS network.

FIGURE 1
Connect through AWS Private Link (Interface Endpoint)
The following diagram shows how instances access AWS services through AWS PrivateLink. First, you create an interface VPC endpoint, which establishes connections between the subnets in your VPC and an AWS service using network interfaces. Traffic destined for the AWS service is resolved to the private IP addresses of the endpoint network interfaces using DNS, and then sent to the AWS service using the connection between the VPC endpoint and the AWS service.
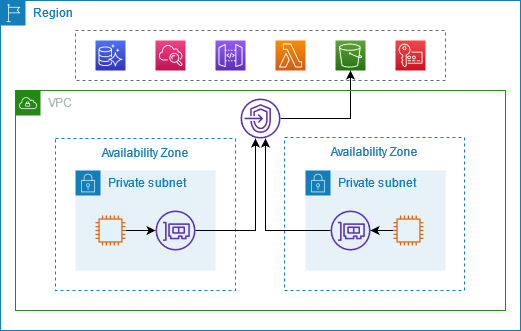
FIGURE 2
AWS services accept connection requests automatically. The service can’t initiate requests to resources through the VPC endpoint.
